Networking and Internet Class 11 Notes helps to understand how modern technology is used in day-to-day life. Networks are the interconnection of multiple computers; networks help to exchange the data and resources globally. A network is the foundation of the Internet. The internet links multiple computers worldwide for communication and resource sharing. In this chapter you are going to learn about the evolution of networks and the internet, computer networks, network communication, transmission medium, types of networks, topology, and different types of terms used in networks and the internet.
Networking and Internet Class 11 Notes
Evolution of Networks and Internet
The idea of the Internet was developed in 1969, and since then, it has undergone a number of technological and infrastructure modifications, as will be explained below:
- 1876: In 1876, Alexander Graham Bell introduced the concept of communication through telephone lines and the development of the Public Switched Telephone Network (PSTN) in 1877.
- 1950: In 1950, the military started communication using the telephone; this method is known as circuit switching.
- Could War Era: The U.S. Department of Defence wanted to create a strong network system, which led to packet switching. In packet switching, the message is broken down into small packets.
- 1969: The US Department of Defence needed the network system for academic and research, which led to the development of the Advanced Research Projects Agency Network (ARPANET). in 1969. ARPANET made use of technology called digital packet switching.
- 1970: A new system was introduced, which is known as TCP/IP, which allows connecting different networks to a single network system.
- 1984: For research and education, another big network is created, which is known as NSFNET, which helps the network system to grow rapidly.
- Internet: The internet becomes a global network that connects different network systems without any central boss. The group IETF and ICANN manage the rules and naming system for the internet, like IP addresses and domain names.
- ISP (Internet Service Provider): Private and government started offering internet connection to the people.
- Bandwidth: Bandwidth describes the maximum data transfer rate of a network or Internet connection.
What is Computer Network?
Electronic equipment that exchange data or messages with one another, such as computers, printers, fax machines, and telephones, are referred to as nodes or stations.

a. Sender – The node that is responsible for sending the data.
b. Receiver – The node that is responsible for receiving the data.
c. Message – Message is the information or meaningful data that is being communicated in a structured form.
d. Channel – Channel is the communication medium through which message is transmitted.
What is network communication?
A computer network is made up of a number of connected nodes that communicate over a channel. There are three types of computer network communication:
- Simplex
- half-duplex
- full-duplex
- Simplex – Information can only be transmitted in one way in simplex mode. It is known as a unidirectional mode. The data transferred via numerous fibre optics and satellites in computer networks is straightforward in nature.
- Half-duplex – Only one node at a time can broadcast data in the half-duplex mode, which allows for bidirectional communication between the two nodes. In low-bandwidth situations, this mode is typically used to transfer files between nodes.
- Full-duplex – In full-duplex mode, both communicating parties can send and receive at the same time. NIC (Network Interface Card) supports full-duplex mode.
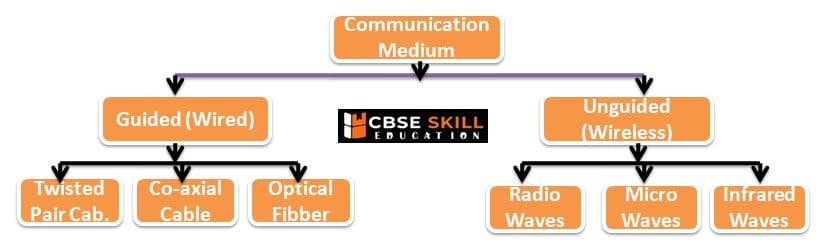
What is transmission medium?
The channel of transmission through which data can be sent as a signal from one node to another is referred to as a transmission medium.
There are two type of transmision medium –
- Guided Medium
- Unguided Medium
- Guided Medium – In guided medium, the data transmitted in a cable system that has a fixed path. for example Co-axil, UTP, Optical fiber cable, etc.
- Unguided Medium – In Unguided medium, the data transmit through free space in the form of electromagnetic signal. for example, radio waves, lasers, micro waves etc.
Different type of network devices
- Repeater – With increase in distance, a signal may become weak and distorted. A repeater is used to restore the input signal to its original form, so that it can travel a larger distance.
- Hub – A hub joins multiple lines, sometimes known as cable segments, as opposed to a repeater which links only two wires. A hub has multiple input/output (I/O) ports, each of which is connected to a single device.
- Bridge – In order to create a larger local area network (LAN), smaller LANs can be combined using bridges, which are multiport devices used to connect two or more LANs.
- Switch – Switches are used to connect individual nodes in the network with one another, as opposed to bridges, which join two or more LAN segments.
- Router – Routers are used to link different networks (LAN or WAN) collectively. Data from an incoming network is sent to another network via a router. A router keeps track of different networks’ routing tables. The router chooses which network the incoming packet should be sent to based on the destination address.
- Gateway – A gateway enables communication across networks based on various protocol systems. Data from one network that uses one protocol is translated to the outgoing network’s protocol before being forwarded.
Different type of Network
On the basis of geographical span, network can be broadly categorized as PAN, LAN, MAN, and WAN.
- Personal area network – An individual’s workspace can be connected to a computer network called a personal area network (PAN) . for example, connection between PCs and smartphone, PCs and tables, PCs and printer etc.
- Local area network – Local Area networks are private networks and can span a radius of up to 1 Km. They are generally established within a building or campus. LANs operate at a speed in the range 10 Mbps to 1 Gbps.
- Metropolitan Area Network – These networks, which have a radius of up to 50 km, are used to create connections within cities. Resources can be shared more easily because to MANs, which link different local area networks. a city-based cable television network, as an example.
- Wide Area Network – A WAN typically covers a distance of roughly 1000 km. They are useful for linking isolated places and for long-distance communication. They create connections inside a nation or continent. A WAN may be owned and operated by a number of different companies. It links numerous metropolitan and local area networks.
What are the different types of topology and types?
Network topology refers to the positioning of nodes in a network, often known as their layout. or the arrangement of nodes in a network is called network topology. there are two type of topologies –
- Broadcast: All nodes share the same physical link one node transmit and other receive. for example, Bus and Ring topologies.
- Point to point: Every pair of nodes has a dedicated link. for example, Star, Mesh and tree topologies.
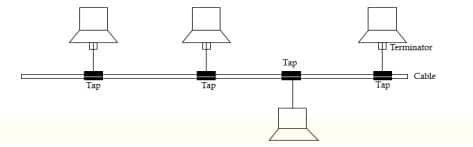
Bus Topology
In a bus topology, several nodes are connected by a lengthy cable known as the backbone cable (or just the backbone) using a connector known as the tap. This topology requires less cabling and is easy to install and extend the network laid using it. However, fault detection and isolation is difficult.
Ring Topology
In a ring topology, all devices are connected by a cable that forms a ring. The intended recipient of the message is reached by way of a one-way transmission of the intended message. The problem of network is it take longer time to send a message from one node to another node.

Star Topology
All of the devices in a star topology are connected to the hub, which serves as the central controller. Any two devices can communicate with each other through the hub that relays messages. Installation and configuration of the star network are simple.

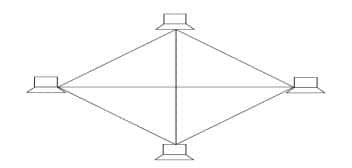
Mesh Topology
In a mesh topology, every node in the network is linked to every other node. The topology offers secure data transfer without any traffic issues because every conceivable pair of nodes has a dedicated point-to-point connection.
Tree Topology
A hybrid topology that combines bus and star topologies is called tree topology. In a bus topology, the primary backbone cable functions as the tree’s trunk, and star networks (and even individual nodes) are connected to it like the tree’s branches.

Identification of computers and users over a network
MAC Address
A network interface controller (NIC) is given a media access control address (MAC address), which it can use as a network address in communications inside a network segment. Ethernet, Wi-Fi, and Bluetooth are just a few of the IEEE 802 networking technologies that frequently employ this application.
MAC addresses are 12-digit hexadecimal (or 48 bit) numbers. By convention, MAC addresses are usually written in one of the following two formats:
- MM:MM:MM: SS: SS:SS
- MM-MM-MM-SS-SS-SS
IP Address
Every computer in a network has an additional unique identification code called an IP Address. The four bytes (or 32 bits) that make up an IP address can range in value from 0 to 255. A typical IP address appears as follows:
- Example: 59.177.134.72
IP addresses are typically written in decimal format as a “dotted decimal number” like the one above to make them simpler for humans to remember.
Domain Name
An Internet physical IP address is linked to an easy-to-remember name known as a domain name, which is frequently just referred to as a domain. It is the distinctive name that follows the @ symbol in email addresses and the www. prefix in web addresses.
Names and Country-Specific Domain Names. For example Generic Domain Names:
- ·com – commercial business
- ·edu – Educational institutions
- ·gov – Government agencies
- ·mil – Military
- ·net – Network organizations
- ·org – Organizations (nonprofit)
Country Specific Domain Names:
- .in – India
- ·au – Australia
- ·ca – Canada
- .ch – China
- .nz – New Zealand
- .pk – Pakistan
- .jp – Japan
- .us – United States of America
Domain Name Resolution
The process of turning a domain name into an IP address is known as domain name resolution. Since one IP address can correlate to many domain names and one domain name to one IP address, multiple domain names can simultaneously be resolved to the same IP address.
Internet and its Terminology
Digital literacy
The capacity to use reading, writing, technological expertise, and critical thinking to navigate our digital world is known as digital literacy. It involves using technology to find, assess, and transmit information, including devices like a smartphone, PC, e-reader, and more.
Internet Services
Network services are programmes that are hosted by servers on a computer network and offer functionality to network users. The Internet has several uses, including e-mail, file sharing, remote login, and the World Wide Web (WWW).
- Electronic Mail (E-Mail) – A multimedia attachment, such as text, audio, an image, or a video, may be included with an email in addition to being a textual message. The email may be sent to one or more intended recipients by the sender.
- File Transfer – FTP is used to transfer files from one computer to another using a TCP-based network (File Transfer Protocol). Client-server architecture is the foundation of File Transfer Protocol.
Local hosts (clients) can download or upload files to distant hosts using FTP (server). - Remote Login (TELNET) –The acronym for this network is TELNET. It is a client-server programme that enables users to connect to remote systems while logged in to one system.
- World Wide Web (WWW) – The World Wide Web (WWW), also referred to as the “web,” is a collection of connected information stored on devices that are dispersed across the Internet.
Internet Protocol Suite
Protocol is set of rule, The common network model and communication protocol stack used on the Internet and in the majority of other computer networks is known as the Internet Protocol Suite (IP suite). The IP suite is largely the global standard for computer-to-computer communication, despite the existence of alternate networking paradigms.
These sub-tasks or functions are performed by different layers of TCP/IP mode
Application layer
Data or a message is formed at the sending end and reviewed and processed at the receiving end. The message that will be sent with the header must likewise be enclosed by this layer. On this layer, a number of protocols like HTTP (HyperText Transfer Protocol) and POP3 (Post Office Protocol version 3) operate.
Transport layer
The message is sent from the application layer to the transport layer, which appends the source and destination ports of the processes at the two ends. At this layer, two end-to-end protocols—TCP and UDP—are in use. When timely and error-free data transport is crucial, TCP (Transmission Control Protocol) is a dependable connection-oriented protocol that is required.
Internet Layer
The Internet layer receives the segments from the transport layer and adds the source and destination machine network addresses (also termed IP address). IP, or Internet Protocol, is utilised at the Internet layer. The format of packets sent over the Internet is specified by IP.
Link layer
Host to Internet layer is another name for link layer. The header containing the sender and receiver physical addresses must be included by this layer to the packet that was received from the Internet layer.
Cyber Threats and Cyber Security
Malwares
Malicious software (programmes) created with the purpose of interfering with system performance by harming the system, gaining unauthorised access to the system, or preventing legitimate users from using computing resources are referred to as malware. Malware includes viruses, worms, and Trojan horses.
- Virus – A virus is a software code that may harm your system by overwriting or corrupting the system files.
- Worm – A worm is often received via network, and it automatically keeps on creating several copies of itself on the hard disk thereby flooding the hard disk. When a worm is received as an email attachment, it is automatically forwarded to the recipients leading to network congestion.
- Trojan Horse – Trojan Horse is a code that appears to be desirable and useful but ends up harming the
system. Trojan horse can attach itself with a safe application. For example, it may be attached to any game downloaded over the Internet. Such an application when executed creates a backdoor in the system through which a hacker can access the system.
Eavesdropping
The act of surreptitiously or covertly listening to another person’s private discussion or communications without that person’s agreement is known as eavesdropping. Telephone lines, cellphone networks, email, and instant messaging are all used for eavesdropping.
Denial of Service
A cyberattack known as a denial-of-service (DoS) attack renders a system or network resource inaccessible to its users by temporarily or permanently interrupting services.
Phishing
The practise of stealing a user’s personal information through fraudulent mail is known as phishing.
These emails either include embedded forms that request personal information from you or include links to web pages that might ask you for it.
Cyber Crime
Cybercrimes are crimes including theft, fraud, and forgery that involve the improper use of computers or the Internet. According to the IT Act, cybercrime is any illegal activity in which a computer is either a tool, a target, or both. These crimes include some of those listed below –
- Cyber bullying – Harassment or bullying inflicted through the use of electronic or communication devices such as computer, mobile phone, laptop, etc.
- Cyber stalking – Use of electronic communication by a person to follow a person or attempts to contact a person to foster personal interaction repeatedly despite a clear indication of disinterest by such person.
- Online Job Fraud – An attempt to defraud people who need employment by giving them a false hope/ promise of better employment with higher wages.
- Vishing – To seek personal information like Customer ID, Net Banking password, ATM PIN, OTP, Card expiry date, CVV etc. through a phone call.
- SMSing – Use of mobile phone text messages to lure victims into calling back on a fraudulent phone
number, visiting fraudulent websites or downloading malicious content via phone or web. - SIM Swap Scam – Getting a new SIM card against a registered mobile number
- Credit card (or debit card) fraud – An unauthorized use of another’s credit or debit card information for the purpose of purchases or withdrawing funds from it.
- Identity theft – Dishonestly making use of the electronic signature, password or any other unique
identification feature of any other person. - Spamming – Persuading a recipient to buy a product or service, or visit a website via email, SMS, MMS
where he can make purchases. - Ransomware – The victim is asked to pay the demanded ransom to get his device decrypts.
Network Security Tools and Services
Network layer security
TCP/IP protocols may be secured with cryptographic methods and security protocol like Secure Sockets Layer (SSL).
Firewalls
An organization’s previously set security policies are used to monitor and filter incoming and outgoing network traffic through a firewall, a network security device. A firewall is essentially the barrier that stands between a private internal network and the open Internet at its most basic level.
Antivirus
Viruses and other types of dangerous software can be found and eliminated from your computer or laptop using an antivirus package. Malicious software, also referred to as malware, is computer code that can damage your computers, laptops, and the data they contain.
Password managers
A password manager is a piece of software that aids in organising and storing passwords. In order to access their complete password database from top to bottom, users of password managers typically need to generate a master password, which should be a single, extremely strong password.
Cyber Law
Cyber laws serve as a deterrent to illicit cybercrime and regulate the systematic use of e-resources, such as e-business. To prevent cybercrimes and prosecute those responsible, numerous cyber laws have also been passed. These laws specify the punishment that will be meted out to those who violate the laws.
Employability Skills Class 11 Notes
- Unit 1 : Communication Skills Class 11 Notes
- Unit 2 : Self-Management Skills Class 11 Notes
- Unit 3 : Information and Communication Technology Skills Class 11 Notes
- Unit 4 : Entrepreneurial Skills Class 11 Notes
- Unit 5 : Green Skills Class 11 Notes
Employability Skills Class 11 MCQ
- Unit 1 : Communication Skills Class 11 MCQ
- Unit 2 : Self-Management Skills Class 11 MCQ
- Unit 3 : Information and Communication Technology Skills Class 11 MCQ
- Unit 4 : Entrepreneurial Skills Class 11 MCQ
- Unit 5 : Green Skills Class 11 MCQ
Employability Skills Class 11 Questions and Answers
- Unit 1 : Communication Skills Class 11 Questions and Answers
- Unit 2 : Self-Management Skills – III
- Unit 3 : Information and Communication Technology Skills Class 11 Questions and Answers
- Unit 4 : Entrepreneurial Skills Class 11 Questions and Answers
- Unit 5 : Green Skills Class 11 Questions and Answers
Information Technology Class 11 Notes
- Unit -1 : Computer Organization Class 11 Notes
- Unit -2 : Networking And Internet Class 11 Notes
- Unit-3 : Office Automation Tools Class 11 Notes
- Unit-4: RDBMS Class 11 Notes
- Unit-5: Fundamentals of Java Class 11 Notes
Information Technology Class 11 MCQ
- Unit -1 : Computer Organization Class 11 MCQ
- Unit -2 : Networking And Internet Class 11 MCQ
- Unit-3 : Office Automation Tools Class 11 MCQ
- Unit-4: RDBMS Class 11 MCQ
- Unit-5: Fundamentals of Java Class 11 MCQ
Information Technology Class 11 Questions and Answers
- Unit -1 : Computer Organization Class 11 Questions and Answers
- Unit -2 : Networking And Internet Class 11 Questions and Answers
- Unit-3 : Office Automation Tools Class 11 Questions and Answers
- Unit-4: RDBMS Class 11 Questions and Answers
- Unit-5: Fundamentals of Java Class 11 Questions and Answers
Disclaimer: We have taken an effort to provide you with the accurate handout of “Networking and Internet Class 11 Notes“. If you feel that there is any error or mistake, please contact me at anuraganand2017@gmail.com. The above CBSE study material present on our websites is for education purpose, not our copyrights. All the above content and Screenshot are taken from Information Technology Class 11 CBSE Textbook, Sample Paper, Old Sample Paper, Board Paper and Support Material which is present in CBSEACADEMIC website, This Textbook and Support Material are legally copyright by Central Board of Secondary Education. We are only providing a medium and helping the students to improve the performances in the examination.
Images and content shown above are the property of individual organizations and are used here for reference purposes only.
For more information, refer to the official CBSE textbooks available at cbseacademic.nic.in
